Are Instagram Influencers Really a Target for Hackers?
Yes, Instagram influencers are high-value targets because of their visibility, brand deals, and the personal data they share.
The mistakes Instagram influencers make often open the door for hackers. Weak passwords, oversharing, fake collaborations, and unsafe apps give attackers multiple ways to steal accounts or personal details. Hackers see influencers as valuable because their accounts can be sold, misused for scams, or leveraged to reach thousands of followers.
Phishing DMs, fake verification messages, malware-infected contracts, and insecure Wi-Fi are among the most common tricks. Many influencers underestimate these threats because they focus more on content than on account safety.
This is why Instagram influencers security has become such an important concern in 2025. Hackers are targeting influencers because one mistake can lead to financial loss and reputational damage.
With this in mind, let us look at the 23 mistakes that explain why hackers target influencers.
👉 Learn structured safety practices through a Cyber Security Certification for stronger protection.
What Password Mistakes Put Instagram Influencers at Risk?
The most common password mistakes Instagram influencers make put their accounts directly at risk.
Mistake 1: Using weak or common passwords
- Hackers often use brute force attacks and leaked password databases.
- Simple passwords like “123456,” “password,” or “iloveinstagram” are guessed within seconds.
- Strong passwords should combine uppercase, lowercase, numbers, and special characters.
Mistake 2: Reusing the same password across accounts
- Many influencers use one password for Instagram, email, and other platforms.
- If one platform suffers a breach, hackers instantly gain access to multiple accounts.
- Password managers are safer for handling unique logins.
Mistake 3: Not enabling two-factor authentication (2FA)
- Without 2FA, a stolen password leads to instant account takeover.
- With 2FA, even if the password leaks, the hacker cannot log in without the extra verification code.
- Instagram offers easy 2FA setup via authentication apps or SMS.
These password mistakes influencers make are basic but dangerous. Many influencers still underestimate how easily hackers exploit poor password habits. The lack of 2FA, in particular, remains one of the biggest reasons why accounts get stolen.
By avoiding weak Instagram passwords, reusing credentials, or ignoring 2FA, influencers can cut off one of the simplest attack routes. Password security is the first and strongest line of defense for any account.
How Do Fake Brand Collaborations Trick Influencers?
Hackers exploit fake brand collaborations on Instagram to steal accounts and personal data.
Mistake 4: Clicking links in fake brand collab DMs
- Hackers send messages pretending to be from well-known brands.
- The links inside often lead to phishing sites that mimic Instagram or brand portals.
- Once influencers enter their login details, hackers gain access instantly.
Mistake 5: Downloading unverified collaboration contracts
- Hackers send PDF or Word documents disguised as contracts.
- These often contain spyware, trojans, or hidden malware that infects devices.
- Safe practice is to scan all files before opening and verify the sender.
Mistake 6: Trusting offers that seem too good to be true
- Unrealistic offers, like being paid thousands for a single post, often mask scams.
- Hackers use urgency to pressure influencers into acting quickly without checking authenticity.
Fake brand collaborations Instagram scams are widespread because influencers want to grow and monetize quickly. Falling for these Instagram collab scams can cost them their accounts and credibility.
The safest approach is to verify every offer directly through brand websites or official emails. No genuine brand will force you into quick clicks or unverified downloads.
Why Is Oversharing Personal Information Dangerous?
Oversharing on Instagram makes influencers an easy target for hackers.
Mistake 7: Posting home addresses or personal contact details
- Hackers can use this information to bypass security questions or plan targeted attacks.
- Even small details like neighborhood tags can expose identity.
Mistake 8: Sharing travel plans in real time
- When influencers share flights or vacations live, hackers know when devices are unattended.
- This timing gives attackers opportunities to launch account takeovers.
Mistake 9: Revealing family or close friends’ private data
- Hackers often target people close to influencers through phishing or impersonation.
- Information about family members can be used for social engineering attacks.
These influencer privacy mistakes are common because many want to connect personally with followers. But the mistakes Instagram influencers make in oversharing often become direct entry points for hackers.
The safer approach is to delay posting travel updates, keep addresses private, and avoid exposing family details. Protecting personal data online is as critical as protecting account passwords.
How Do Hackers Exploit Phishing and Verification Scams?
Hackers use phishing and fake verification scams on Instagram to trick influencers into giving away their account credentials.
Mistake 10: Falling for fake Instagram “verification” DMs
- Hackers pretend to be from Instagram, offering a blue check.
- These messages often contain links to phishing pages.
- Once influencers enter details, the hacker takes over the account.
Mistake 11: Clicking on phishing links promising account recovery
- Fake recovery pages look almost identical to Instagram’s real login.
- Hackers use these sites to harvest usernames and passwords.
- Real recovery links always come from official Instagram domains.
Mistake 12: Ignoring warning signs in suspicious messages
- Misspelled words, urgent demands, or non-official email addresses are red flags.
- Many influencers skip checking these details and end up compromised.
These Instagram phishing scams remain among the most effective ways hackers steal accounts. Scammers know influencers care deeply about verification and recovery, which makes them easy bait.
Avoiding fake Instagram verification attempts requires awareness. Always double-check links, and never trust unsolicited verification offers. Instagram never sends verification through random DMs.
What Device and Network Mistakes Make Influencers a Target?
Device and network mistakes Instagram influencers make often expose them to hackers without realizing it.

Mistake 13: Using public Wi-Fi without VPN
- Hackers intercept traffic on public Wi-Fi at airports, cafes, or hotels.
- Login details and private chats can be stolen.
- Using a VPN secures the connection and keeps data private.
Mistake 14: Not updating phone and app software
- Outdated apps contain security flaws hackers exploit.
- Many malware attacks succeed because devices lack updates.
- Regular updates patch vulnerabilities and close loopholes.
Mistake 15: Saving passwords in plain text on devices
- Some influencers keep notes with passwords on their phones.
- If a device is stolen or hacked, accounts are instantly exposed.
- Password managers are safer alternatives.
These device security for influencers issues are critical. Hackers actively target those using insecure Wi-Fi Instagram logins or devices without updates.
Fixing these habits drastically reduces the chances of being hacked. A secure device and safe network are as important as strong passwords.
How Do Free Tools and Apps Put Influencers at Risk?
Unsafe apps and free tools are one of the biggest risks for Instagram influencers.
Mistake 16: Downloading free follower-tracking apps
- Many apps promise to boost followers or track engagement.
- In reality, they harvest login details or install spyware.
- Hackers then sell stolen accounts on black markets.
Mistake 17: Using unauthorized Instagram analytics tools
- Third-party tools often require login credentials.
- These tools may violate Instagram’s policies and expose accounts.
- Hackers exploit them to bypass protections.
Mistake 18: Granting unnecessary permissions to random apps
- Apps often request access to photos, contacts, or even full device data.
- Once granted, hackers can view sensitive information.
- Always check app permissions before installing.
These unsafe Instagram apps are widely advertised but rarely safe. Influencers chasing quick growth often ignore the risks, falling for these free follower apps risk traps.
The safer path is to rely only on official Instagram features or approved partner apps. Learning through structured training such as Certified Ethical Hacking helps influencers understand how attackers abuse these tools.
What Posting Habits Help Hackers?
Posting mistakes Instagram influencers make often reveal more than intended, giving hackers easy opportunities.

Mistake 19: Posting photos with sensitive information in the background
- Items like ID cards, credit cards, or boarding passes may be visible.
- Hackers zoom into these details and misuse them for fraud.
Mistake 20: Geotagging posts with current location
- Real-time geotags alert hackers or stalkers to where influencers are.
- This information can be used for both digital and physical threats.
Mistake 21: Oversharing behind-the-scenes brand details
- Posting unreleased campaigns or private business info helps hackers craft scams.
- Attackers impersonate brands to trick followers or the influencer themselves.
These geotagging Instagram risks and other posting oversights may seem harmless but are exploited daily by hackers. Every piece of information online can be pieced together to plan attacks.
By avoiding these posting mistakes influencers make, they protect not only themselves but also their audience from being dragged into scams. Posting smarter is just as important as posting often.
What Email Mistakes Linked to Instagram Hacks Do Influencers Make?
Email mistakes influencers make often open the first door for hackers to steal Instagram accounts.
Mistake 22: Using personal email for Instagram logins
- Personal emails are easier to guess or already leaked in past breaches.
- If a personal inbox is hacked, attackers reset Instagram passwords easily.
- Using a dedicated business email for accounts adds an extra layer of security.
Mistake 23: Falling for fake password reset emails
- Hackers send emails that mimic official Instagram notifications.
- The links lead to phishing sites designed to capture login details.
- A quick check of the sender address and URL can expose the fraud.
These Instagram email scams are among the simplest yet most effective attacks. Influencers receive hundreds of messages daily, making it easy to overlook small red flags.
Avoiding email mistakes influencers make requires caution. Always verify the sender, avoid clicking on suspicious links, and enable email two-factor authentication for added safety.
What Are the Consequences of These 23 Mistakes?
The consequences of Instagram hacking are severe and can damage both personal and professional lives.
Key risks for influencers include:
- Loss of account access – stolen accounts are sold on black markets.
- Financial theft – hackers redirect brand payments or scam followers.
- Reputational damage – scams run from a hacked account hurt trust.
- Personal safety risks – overshared data can lead to stalking or identity theft.
The risks for influencers go beyond just losing followers. Many hackers exploit access for long-term fraud, selling personal data or using accounts in wider cybercrime networks.
By understanding the consequences of Instagram hacking, influencers can see why prevention is more effective than recovery. Once control is lost, getting an account back may take weeks or may never happen.
How Can Instagram Influencers Stay Safe from Hackers?
Instagram safety tips are simple but powerful when followed consistently.
Practical steps include:
- Use strong, unique passwords for all accounts.
- Enable two-factor authentication for added protection.
- Avoid clicking suspicious links in DMs or emails.
- Keep apps and devices updated to patch security flaws.
- Use a VPN when logging in on public Wi-Fi.
- Limit oversharing of personal details or location tags.
These measures help influencers understand how influencers protect accounts effectively. By combining strong security habits with awareness of scams, most common attacks can be avoided.
For advanced learning, enrolling in structured training such as the C|EH v13 Ethical Hacker Course builds professional-level defensive skills that protect not only personal accounts but also brand collaborations.
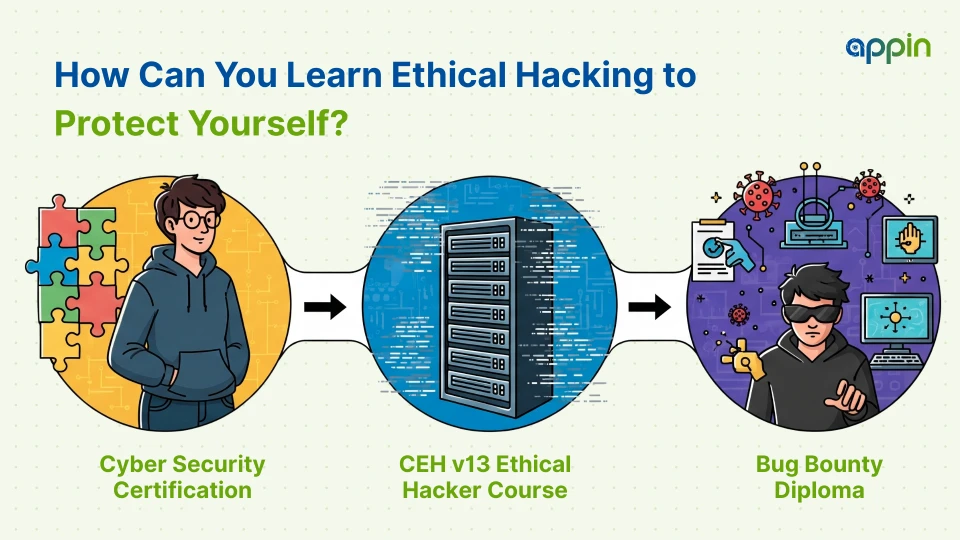
How Can You Learn Ethical Hacking to Protect Yourself?
The safest way to understand hacker tactics is by learning ethical hacking in a controlled environment.
Influencers and students can explore:
- Cyber Security Certification – learn the foundations of account safety and secure practices.
- C|EH v13 Ethical Hacker Course – gain advanced penetration testing knowledge with real-world labs.
- Bug Bounty Diploma – practice hands-on vulnerability hunting to see how hackers exploit mistakes.
Studying these courses allows you to understand how ethical hacking skills influencers need can be developed safely. Instead of relying on unsafe tools or guesswork, learners practice in labs and simulations where there are no risks.
If you want to learn ethical hacking for Instagram protection, these structured paths are the right way forward. They transform curiosity into skill and prepare you to defend against actual attacks.
Should Instagram Influencers Worry About Hackers?
Yes, Instagram influencers should worry about hackers because their visibility and brand value make them frequent targets.
The mistakes Instagram influencers make often appear small, like weak passwords, unsafe apps, or oversharing personal data. But hackers exploit these small openings to take over accounts, steal money, and damage reputations.
By avoiding the 23 mistakes outlined here, influencers can reduce risks significantly. Secure passwords, two-factor authentication, cautious app use, and smarter posting habits make a big difference.
So, are Instagram influencers safe? They can be, but only if they adopt strong digital habits and learn how hackers operate. Structured learning through certifications and safe labs ensures that knowledge is applied responsibly.
The safest approach is prevention. If you are serious about protecting your digital identity, now is the time to act.
👉 Inquire now with Appin to start your cybersecurity journey and keep your accounts secure.


