Ransomware Attack Explained: How It Works + Detection & Response Steps (SOC + Blue Team)
A ransomware attack explained in simple terms is a malware attack that locks or encrypts data and demands payment to restore access.
For students and fresh graduates in India, understanding how ransomware works is essential because SOC teams handle these incidents daily. This guide explains how ransomware attacks happen, how detection works, and how Blue Teams respond in real scenarios.
If you want to build a career in cybersecurity, learning ransomware detection and response skills is a strong starting point.
What Is a Ransomware Attack in Cybersecurity?
A ransomware attack is a type of malware that encrypts files or systems and demands money to unlock them.
When people search for ransomware attacks, they usually want to understand how attackers lock data and why companies panic. Ransomware is not just a virus. It is a targeted cyber attack that disrupts business operations.
In cybersecurity, ransomware:
- Encrypts files or entire systems
- Blocks user access
- Displays a ransom note
- Demands payment in cryptocurrency
Unlike basic malware, ransomware directly impacts business continuity. Hospitals, banks, startups, and even educational institutions in India have been targeted.
For SOC analysts, ransomware is treated as a critical incident because data loss and downtime can cost companies crores.

How Does a Ransomware Attack Work Step by Step?
A ransomware attack works through a structured sequence that includes initial access, execution, lateral movement, and encryption.
To understand how ransomware works step by step, you need to see the full attack chain.
Here is the typical ransomware attack process:
- Initial Access
Attackers use phishing emails, malicious attachments, or vulnerable software to gain entry. - Execution
The malware runs inside the system after the user clicks a link or opens a file. - Privilege Escalation
Attackers try to gain admin access to control more systems. - Lateral Movement
The malware spreads across the network to infect multiple machines. - Data Encryption
Files are encrypted using strong cryptographic algorithms. - Ransom Note
A message appears demanding payment for decryption.
| Stage | What Happens | SOC Focus |
| Initial Access | Phishing or exploit | Monitor unusual logins |
| Execution | Malware runs | Detect suspicious processes |
| Lateral Movement | Spread in network | Track abnormal traffic |
| Encryption | Files locked | Trigger incident response |
Understanding this process is critical for ransomware detection techniques used by Blue Teams.
What Role Does a SOC Analyst Play During a Ransomware Attack?
A SOC analyst monitors alerts, analyzes suspicious activity, and escalates ransomware incidents before major damage occurs.
The SOC analyst role in ransomware attack situations is primarily defensive. Their job is to detect early signs before encryption spreads.
During a ransomware incident, a SOC analyst:
- Monitors SIEM dashboards
- Reviews unusual login attempts
- Investigates abnormal file activity
- Checks endpoint alerts
- Escalates confirmed threats
In India, many entry level cybersecurity professionals begin their career as SOC L1 analysts. This role builds strong experience in log analysis and incident response.
A ransomware attack explained in interviews often includes questions about how SOC teams detect early encryption behavior. Recruiters expect freshers to understand monitoring tools and alert prioritization.
SOC job responsibilities in India increasingly focus on real time monitoring and quick escalation to reduce damage.
How Do Blue Teams Detect Ransomware Attacks in Real Time?
Blue Teams detect ransomware using log analysis, endpoint monitoring, and anomaly detection tools.
Ransomware detection techniques rely on continuous monitoring of systems and networks. Detection must happen before full encryption spreads.
Common detection methods include:
- SIEM log monitoring
- Endpoint detection tools
- File integrity monitoring
- Suspicious PowerShell activity detection
- Abnormal network traffic analysis
Popular tools used in SOC environments:
| Tool | Purpose |
| Splunk | Log analysis and alerting |
| Wazuh | Open source security monitoring |
| Microsoft Defender | Endpoint protection |
| CrowdStrike | Advanced threat detection |
Blue team skills for ransomware include understanding how encryption behavior looks inside system logs.
When ransomware attack explained in practical labs, students learn to identify:
- Sudden file modification spikes
- Disabled antivirus services
- Unauthorized privilege escalation
These skills are essential for anyone preparing for a SOC analyst career in India.
What Are the Early Warning Signs of a Ransomware Attack?
Early warning signs of a ransomware attack include unusual login activity, sudden file changes, and disabled security tools.
Knowing the signs of ransomware attack helps SOC teams respond quickly.
Common early indicators include:
- Multiple failed login attempts
- Admin account misuse
- Rapid file renaming or extension changes
- Backup deletion attempts
- Sudden spike in CPU usage
If you want to detect ransomware early, you must monitor both user behavior and system logs.
| Indicator | Why It Matters |
| Failed logins | Possible brute force attempt |
| File changes | Encryption in progress |
| Disabled antivirus | Attacker clearing defenses |
A ransomware attack explained clearly always highlights that early detection reduces damage significantly.
What Are the Immediate Ransomware Incident Response Steps?
The immediate ransomware incident response steps include isolating infected systems, stopping network spread, and preserving evidence.
When ransomware is confirmed, action must be quick and structured.
Here is the standard incident response process in cybersecurity:
- Isolate the Infected System
Disconnect affected machines from the network immediately. - Disable Shared Drives
Prevent further encryption across network resources. - Preserve Logs
Collect logs and forensic evidence for investigation. - Inform Stakeholders
Notify security teams and management. - Activate Incident Response Plan
Follow documented recovery procedures.
SOC teams must not panic or randomly shut systems. Structured response prevents further loss.
Understanding ransomware incident response steps is critical for students preparing for cybersecurity jobs for freshers in India.
A ransomware attack explained from a Blue Team perspective always emphasizes containment before recovery.
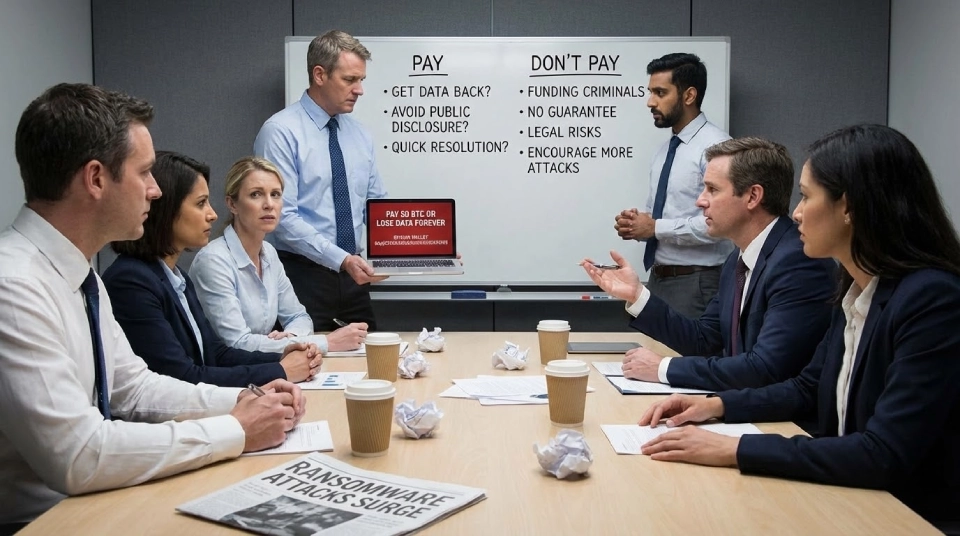
Should Companies Pay the Ransom in a Ransomware Attack?
Security experts generally advise against paying the ransom because payment does not guarantee data recovery.
When companies ask should companies pay ransomware, the answer depends on risk, backups, and legal implications.
Reasons experts discourage payment:
- No guarantee of decryption key
- Encourages future attacks
- Possible legal issues
- Risk of double extortion
Ransomware recovery best practices focus on:
- Regular backups
- Strong endpoint security
- Network segmentation
- Continuous monitoring
A ransomware attack explained in case studies often shows that companies with strong backup strategies recover faster without paying attackers.
What Skills Do You Need to Handle Ransomware Attacks as a SOC or Blue Team Professional?
To handle ransomware attacks, you need strong log analysis skills, network monitoring knowledge, and hands on incident response practice.
SOC skills for freshers in India must focus on practical exposure rather than only theory.
Core technical skills include:
- Log analysis using SIEM tools
- Endpoint monitoring
- Understanding Windows and Linux systems
- Network traffic analysis
- Incident response documentation
Students who want structured learning paths often enroll in cybersecurity certification programs to build foundational knowledge.
Practical exposure through certified ethical hacking training helps students understand attacker techniques and defensive strategies.
Advanced learners can explore the CEH v13 AI powered course to understand modern threat detection and AI based security analysis.
Those interested in vulnerability discovery and responsible disclosure can strengthen their skills through a bug bounty diploma program, which builds hands on security testing experience.
A ransomware attack explained during lab simulations gives students confidence to handle real incidents in SOC environments.
How Can Students in India Start a Career in SOC and Blue Team Security?
Students in India can start a SOC analyst career by building cybersecurity fundamentals, practicing in labs, and applying for entry level security roles.
The SOC analyst career in India is growing due to increasing cyber threats across industries.
Step by step career path:
- Learn networking basics
- Understand security fundamentals
- Practice ransomware detection in labs
- Gain certification knowledge
- Apply for SOC L1 roles
Cybersecurity jobs for freshers in India often require:
- Basic knowledge of SIEM tools
- Understanding of incident response
- Awareness of ransomware detection techniques
Entry level SOC salaries in India typically range between 3 to 6 lakh per year depending on skills and city.
Understanding ransomware attack explained concepts prepares students for interviews and practical assessments.
With consistent practice and technical knowledge, students can build stable careers in Blue Team security and security operations centers.


