Active Directory Pentesting Basics: AD Attacks Every Pentester Must Know
Active Directory pentesting is the process of testing and exploiting security weaknesses inside a Windows domain environment.
For students and fresh graduates in India, understanding Active Directory security is essential because most companies use Windows domain networks. If you want to build a penetration testing career in India, you must know how AD attacks work and how enterprise breaches happen.
This guide explains common AD attacks, tools, required skills, and how to start learning them in a practical way.
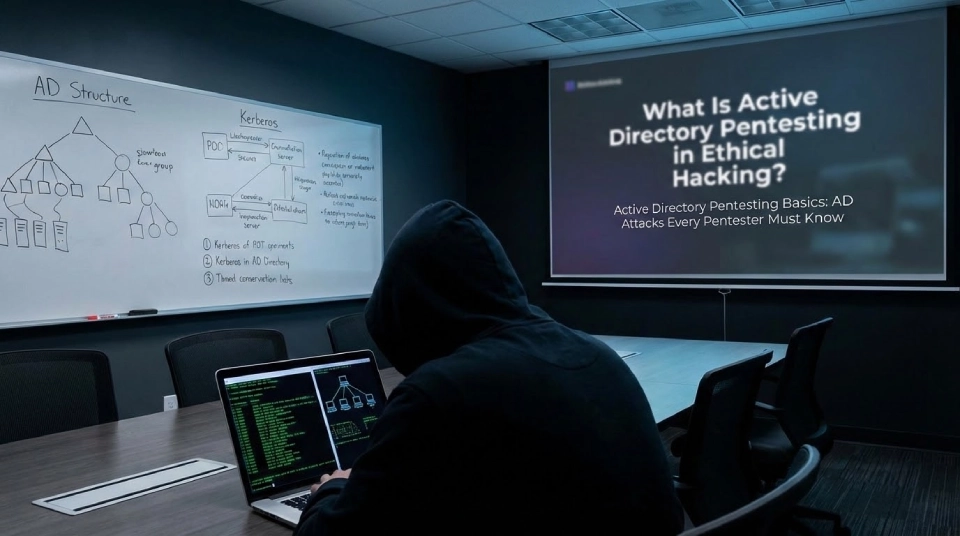
What Is Active Directory Pentesting in Ethical Hacking?
Active Directory pentesting is the process of identifying and exploiting misconfigurations inside Windows domain environments to simulate real enterprise attacks.
When people search for what is Active Directory pentesting, they usually want to understand how attackers gain domain level access. Active Directory controls authentication, user access, and permissions across an organization.
In ethical hacking, AD security testing focuses on:
- Domain controllers
- User account privileges
- Authentication protocols
- Misconfigured permissions
- Credential exposure
Unlike basic network scanning, AD testing targets identity and access management systems.
Most enterprise breaches begin with credential compromise. That is why Active Directory pentesting is considered an advanced and essential penetration testing skill.
Why Do Attackers Target Active Directory in Enterprise Networks?
Attackers target Active Directory because it controls authentication and access across the entire organization.
If attackers compromise a domain controller, they can:
- Access sensitive files
- Create new administrator accounts
- Move across the network
- Disable security controls
Active Directory acts as the backbone of enterprise security. Once compromised, the entire network becomes vulnerable.
| Component | Why It Is Targeted |
| Domain Controller | Central authentication authority |
| Service Accounts | Often have high privileges |
| Admin Groups | Control over multiple systems |
| Kerberos Tickets | Used for authentication |
Understanding why attackers target Active Directory helps students see the importance of AD attacks every pentester must know.
What Are the Most Common AD Attacks Every Pentester Must Know?
The most common AD attacks every pentester must know include Kerberoasting, Pass the Hash, Golden Ticket, Silver Ticket, and DCSync.
These attacks simulate real enterprise breaches and test domain level security.
Common Active Directory attacks include:
- Kerberoasting
- Pass the Hash
- Pass the Ticket
- Golden Ticket attack
- Silver Ticket attack
- DCSync attack
- LDAP enumeration
Each attack focuses on exploiting authentication mechanisms or privilege misconfigurations.
| Attack | Target | Goal |
| Kerberoasting | Service accounts | Crack passwords offline |
| Pass the Hash | NTLM hashes | Lateral movement |
| Golden Ticket | Kerberos | Domain persistence |
| DCSync | Domain controller | Extract password hashes |
During Active Directory pentesting, these techniques are tested in controlled lab environments to evaluate enterprise defenses.
Students preparing for ethical hacking interviews in India are often asked to explain these attack techniques clearly.
How Does Kerberoasting Work in Active Directory?
Kerberoasting works by extracting service account ticket hashes and cracking them offline to obtain passwords.
To understand how Kerberoasting works in Active Directory, you must first understand Kerberos authentication.
The process includes:
- Identify Service Principal Names
- Request service tickets from domain controller
- Extract ticket hashes
- Crack hashes offline using password cracking tools
Service accounts often have weak passwords. Once cracked, attackers gain elevated privileges.
Kerberoasting is one of the most tested techniques during Active Directory pentesting because it demonstrates weak credential management.
Detection involves:
- Monitoring unusual ticket requests
- Identifying abnormal service account usage
- Tracking large volume authentication requests
For penetration testing students, understanding Kerberos basics is critical before learning advanced AD exploitation.
What Is Pass the Hash Attack and How Is It Exploited?
Pass the Hash attack allows attackers to authenticate using stolen NTLM hashes without knowing the original password.
In a pass the hash attack explained scenario, attackers extract NTLM hashes from memory using credential dumping tools.
The steps typically include:
- Gain access to a compromised system
- Dump NTLM hashes from memory
- Reuse the hash to authenticate to another machine
- Move laterally across the network
This technique works because Windows authentication accepts valid hashes instead of requiring plain passwords.
During Active Directory pentesting, testers simulate this attack to evaluate network segmentation and credential hygiene.
Detection methods include:
- Monitoring abnormal authentication patterns
- Detecting credential dumping behavior
- Tracking unusual administrator access
Pass the Hash remains one of the most practical AD attacks in enterprise environments.
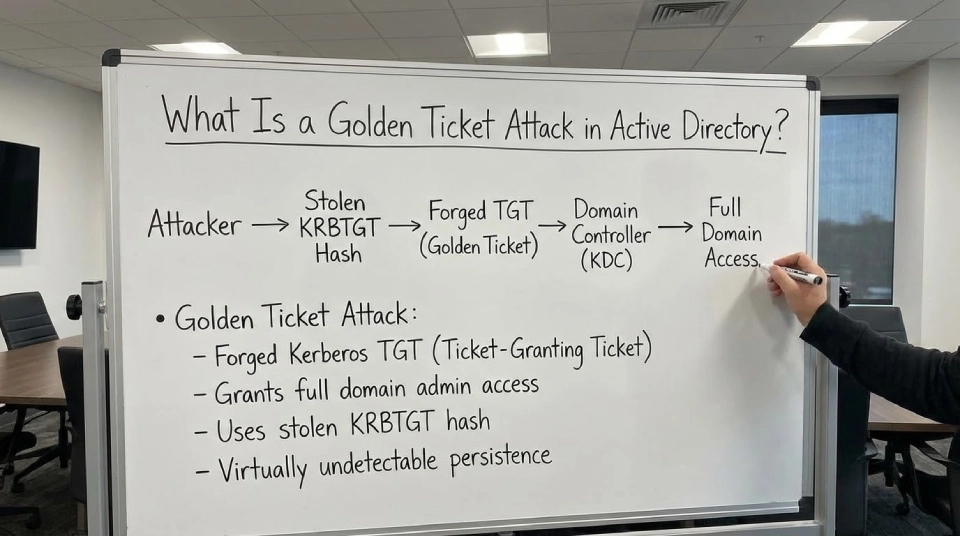
What Is a Golden Ticket Attack in Active Directory?
A Golden Ticket attack allows attackers to create forged Kerberos tickets that grant domain administrator level access.
This attack becomes possible when the KRBTGT account hash is compromised.
The attack process includes:
- Extract KRBTGT hash from domain controller
- Generate forged Kerberos tickets
- Grant unlimited access across the domain
- Maintain long term persistence
Golden Ticket attack in Active Directory is considered severe because it allows full domain compromise.
| Feature | Impact |
| Forged Tickets | Unauthorized access |
| Domain Persistence | Long term control |
| Privilege Escalation | Admin level rights |
During Active Directory pentesting, this technique tests the resilience of domain controller security and monitoring systems.
What Tools Are Used for Active Directory Pentesting?
Active Directory pentesting uses specialized tools for enumeration, credential extraction, and privilege escalation testing.
Common tools include:
- Mimikatz for credential dumping
- BloodHound for privilege mapping
- PowerView for domain enumeration
- Impacket for exploitation scripts
- Rubeus for Kerberos manipulation
These tools help pentesters identify attack paths inside Windows domain environments.
| Tool | Primary Use |
| Mimikatz | Extract credentials |
| BloodHound | Visualize attack paths |
| Impacket | Execute remote attacks |
| Rubeus | Manipulate Kerberos tickets |
Learning these tools is essential for anyone preparing for AD pentesting roles in India.
What Skills Are Required for Active Directory Pentesting in India?
Active Directory pentesting requires strong knowledge of Windows networking, authentication protocols, and privilege escalation techniques.
Students aiming for AD pentesting skills for freshers in India should focus on:
- Networking fundamentals
- Windows operating system internals
- Kerberos and NTLM authentication
- Command line tools
- Log analysis
Practical lab exposure is critical. Structured cybersecurity certification programs help build foundational knowledge in networking and system security.
Hands-on experience through certified ethical hacking training allows students to practice AD attacks in controlled lab setups.
Advanced learners who want to understand modern enterprise defense and attack simulation can explore the CEH v13 AI-powered course to strengthen their authentication attack knowledge.
Those interested in vulnerability discovery and responsible disclosure can improve exploitation skills through a bug bounty diploma program, which builds real world security testing experience.
Active Directory pentesting is considered an advanced penetration testing capability, so consistent practice is essential.
How Can Students in India Start a Penetration Testing Career Focused on Active Directory?
Students in India can start a penetration testing career focused on Active Directory by building fundamentals, practicing in labs, and applying for entry level roles.
To learn how to learn Active Directory pentesting effectively, follow this path:
- Master networking basics
- Understand Windows authentication
- Build a local AD lab using virtual machines
- Practice common AD attacks
- Prepare for penetration testing interviews
Penetration testing career in India is growing rapidly due to increasing enterprise security needs.
Entry level roles often expect:
- Basic knowledge of AD attacks
- Understanding of authentication protocols
- Familiarity with enumeration tools
A strong understanding of Active Directory pentesting concepts helps students stand out in interviews and technical assessments.
With focused learning and lab practice, fresh graduates can transition into ethical hacking and enterprise security roles confidently.


