API Security Testing: Finding Vulnerabilities in REST APIs and GraphQL
API security testing is a way to find weaknesses in the application programming interfaces that can expose data and backend functionality. These days modern applications depend on APIs to connect apps, web services and cloud systems. So security teams do API security testing to detect weaknesses before attackers exploit them.
Research from the Salt Security State of API Security report shows that than 90% of organizations had API security problems in recent years. Businesses use APIs for login systems, payments and data exchange. If the security of these interfaces is weak it can expose customer data and internal services.
Proper testing helps organizations find vulnerabilities early and secure their applications.
What Is API Security Testing?
API security testing is the process of analyzing application programming interfaces to find vulnerabilities that attackers could use to access systems or manipulate data.
APIs allow different software components to communicate with each other. These interfaces often exchange information such as user credentials, financial transactions and application data.
Why APIs are common attack targets
- APIs expose application functionality directly
- Mobile apps communicate with servers using APIs
- Sensitive information often flows through APIs
- Attackers can bypass the user interface. Target APIs
Types of data exposed through APIs
- User authentication details
- Payment information
- Personal account data
- Backend service operations
Security testing helps identify weaknesses that attackers could exploit to retrieve information.

Why Is API Security Testing Important for Modern Applications?
API security testing is important because APIs are now the backbone of modern software systems.
Mobile applications, cloud services and SaaS platforms all rely heavily on APIs to exchange data between services.
Reasons APIs increase security risks
- Each endpoint creates an entry point
- Applications may expose dozens of endpoints
- Internal microservices communicate through APIs
- Third-party integrations increase exposure
Security risks caused by APIs
- Unauthorized access to accounts
- Data exposure through insecure endpoints
- Service abuse by automated bots
- Unauthorized system actions
Organizations that perform testing significantly reduce the chances of API-based data breaches.
How Do Hackers Discover APIs During API Security Testing?
Hackers discover APIs by analyzing application traffic and identifying endpoints that communicate with backend services.
Attackers usually start by observing how an application interacts with its server.
Common API discovery techniques
- Monitoring network traffic in browsers
- Inspecting application requests
- Reviewing developer documentation
- Analyzing JavaScript files
Sources where APIs become exposed
- API documentation
- Application front-end code
- Mobile application traffic
- Automated endpoint scanners
Security testers follow steps when mapping an applications API surface before testing for vulnerabilities.
How Do Authentication Weaknesses Affect API Security Testing?
Authentication weaknesses allow attackers to access API endpoints without identity verification.
Most APIs rely on tokens, API keys or sessions to verify users. Weak validation logic can expose these mechanisms.
Common authentication vulnerabilities
- Token validation
- Exposed API keys in requests
- Improper session management
- Broken authentication workflows
Risks caused by authentication weaknesses
- Account access
- Administrative privilege abuse
- Exposure of sensitive user information
Authentication testing is a part of API security testing because many attacks begin with weak login controls.
How Do Injection Attacks Impact API Security Testing?
Injection attacks occur when APIs process user input without validation.
Attackers manipulate request parameters to execute commands or retrieve sensitive data.
Common injection risks in APIs
- Database query manipulation
- Unsanitized request parameters
- Improper input validation
Weak input handling can allow attackers to execute database queries. Security teams often identify these weaknesses while testing for database exploitation techniques that allow attackers to extract sensitive information from backend systems.
Improper API responses may also expose applications to client-side script injection vulnerabilities related to browser-based attacks that execute malicious scripts inside user sessions .
How Do Broken Access Controls Affect API Security Testing?
Broken access control vulnerabilities allow attackers to access resources that should be restricted.
Many APIs rely on identifiers such as user IDs. Object IDs to retrieve data. Weak authorization checks allow attackers to manipulate these values.
Common access control weaknesses
- Missing authorization validation
- Manipulated object identifiers
- Improper permission checks
Attackers frequently modify identifiers inside API requests to access users data. This type of vulnerability is commonly discussed in security research explaining how attackers manipulate identifiers to retrieve unauthorized information .
Access control testing helps identify these authorization failures before they expose data.
How Do Security Testers Perform API Security Testing?
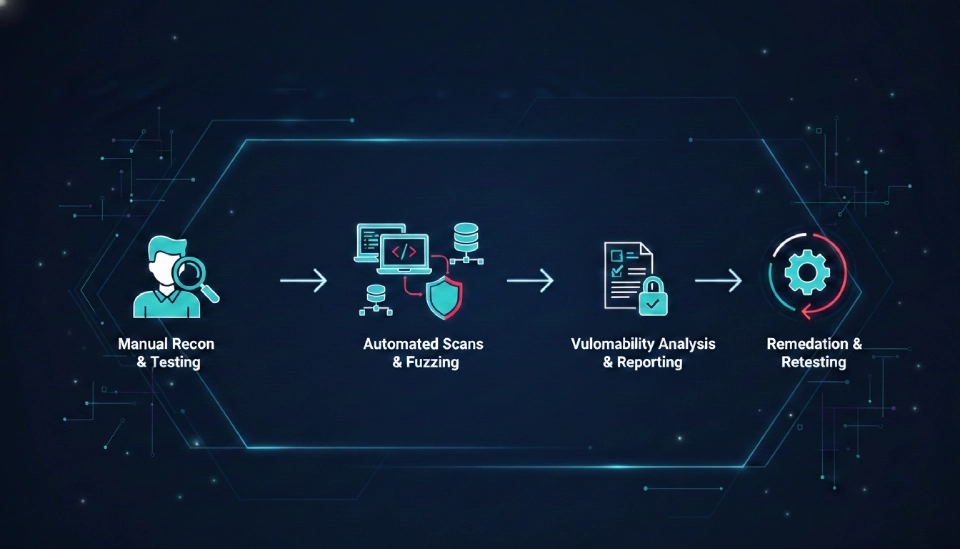
Security testers perform API security testing by analyzing requests manipulating parameters and observing application responses.
Testing typically includes both automated tools and manual analysis.
Common API testing techniques
- Intercepting API requests
- Modifying parameters
- Testing authentication logic
- Analyzing server responses
Security professionals often analyze API traffic using tools designed for intercepting and modifying application requests during penetration testing .
Manual API testing tasks
- Reviewing request structure
- Testing endpoint permissions
- Identifying data exposure issues
- Checking authentication controls
How Can Organizations Prevent API Security Vulnerabilities?
Organizations can prevent API vulnerabilities by implementing authentication and continuous security testing.
Secure API design reduces the risk of data exposure and unauthorized access.
Security practices for APIs
- Strong authentication mechanisms
- Strict authorization validation
- Proper input validation
- API rate limiting and monitoring
API security testing practices
- Penetration testing
- Automated vulnerability scanning
- Continuous security monitoring
Organizations that implement these practices significantly reduce their API attack surface.
Key Takeaways
- API security testing identifies vulnerabilities, in REST APIs and GraphQL services.
- APIs expose application data and functionality.
- Weak authentication and input validation create security risks.
- Injection and access control vulnerabilities frequently affect APIs.
- Regular testing helps organizations protect their API infrastructure.