What Are the 7 Ways Hackers Steal Cryptocurrency in 2026 and How Can You Protect Your Wallet?
Hackers stole over $4 billion in cryptocurrency during 2025 alone, pushing losses to a new all time high according to PeckShield. The FBI recorded $11.36 billion in crypto fraud losses that same year, a 22 percent jump from 2024. Understanding the ways hackers steal cryptocurrency is no longer optional for anyone who owns digital assets. The seven methods covered in this guide represent the most common and damaging threats your wallet faces right now.
Hackers steal cryptocurrency through phishing, malware, fake apps, exchange breaches, social engineering, SIM swapping, and smart contract exploits. Protection includes strong security habits, verified platforms, and using secure wallets.
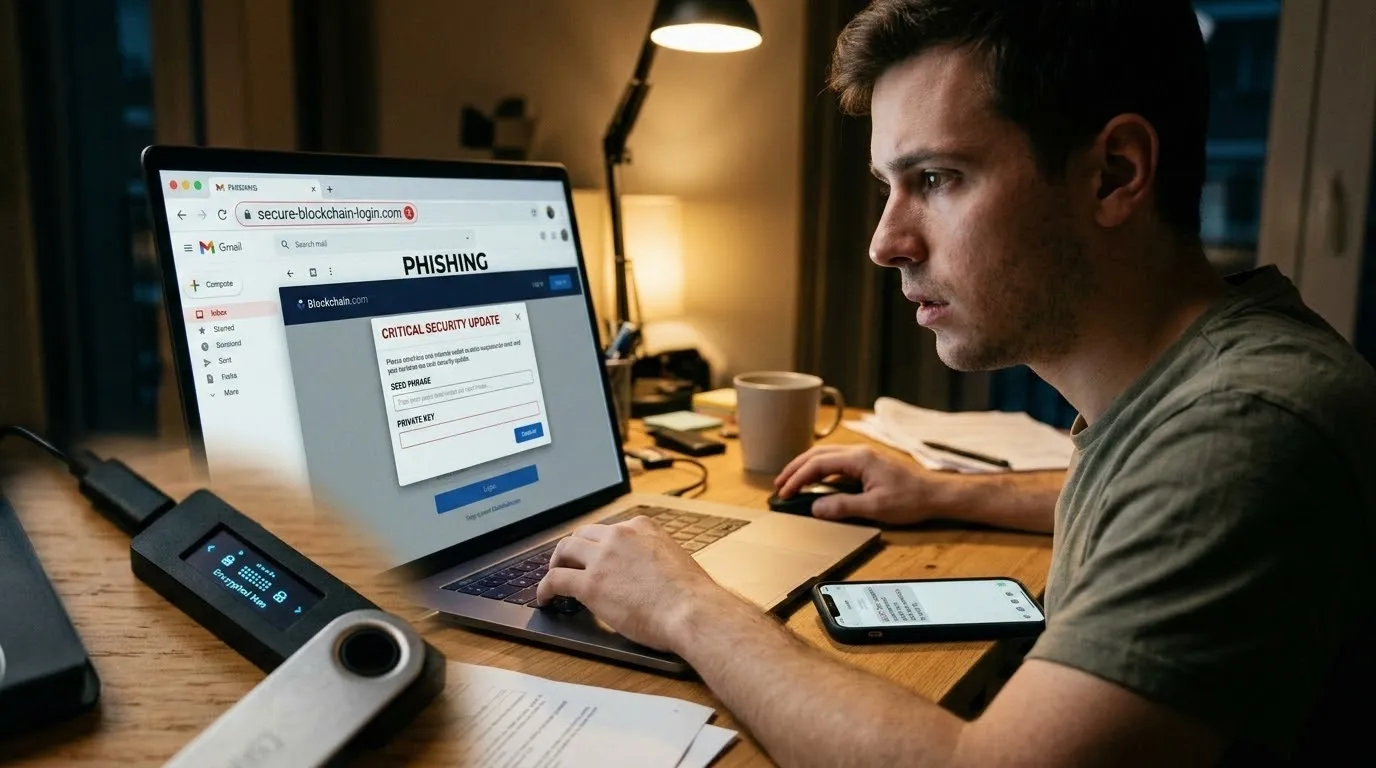
Phishing Attacks Targeting Crypto Wallets
Hackers trick users into entering wallet credentials on fake websites that look identical to real exchanges or wallet providers.
Phishing losses in crypto dropped to $83.85 million in 2025, down 83 percent from nearly $494 million in 2024 according to Scam Sniffer. That drop sounds good, but phishing still affected over 106,000 victims. Attackers now use more convincing fake login pages and target users during periods of high market activity.
How Phishing Works Against Crypto Users
- Fake login pages that copy the design of real exchanges and wallet apps
- Email and SMS messages with urgent warnings about account problems
- Links sent through social media groups or direct messages
- Fraudulent airdrop offers that require connecting your wallet to a malicious site
Strong cryptocurrency security starts with checking every URL before you click. Bookmark your trusted platforms and never enter credentials through links in emails or messages.
Malware That Steals Private Keys
Malicious software secretly extracts private keys and wallet passwords from infected devices, often without the user knowing anything is wrong.
A new strain called MassJacker targeted piracy users in 2025 and was linked to over 778,000 stolen transactions according to The Hacker News. Clipboard hijacking malware swaps wallet addresses you copy, so you send funds straight to the attacker instead of your intended destination.
Types of Crypto Malware to Watch For
- Keyloggers that record every keystroke including passwords and recovery phrases
- Clipboard hijackers that replace wallet addresses during copy and paste
- Trojan apps bundled with fake software downloads
- Crypto mining malware that uses your device resources without permission
Download software only from official sources. Run regular antivirus scans and keep your operating system updated. Cybercrime prevention starts with basic digital hygiene.
Resources:
Fake Crypto Apps and Wallets
Hackers create fake mobile and desktop apps that look like legitimate wallets or exchanges to steal login details and drain user accounts.
Trust Wallet reported that fake wallet apps and copycat token schemes are among the most common threats in 2025. These apps appear in official app stores with names and icons designed to fool even experienced users.
Signs of a Fake Crypto App
- The developer name does not match the official company behind the wallet
- The app asks for permissions it should not need like full device access
- Reviews are mostly generic or overly positive without specific details
- The app redirects you to a different website than the official one
Only download wallet apps from official websites or verified app store pages. Check the developer name and user reviews before installing anything that handles your money.
Exchange Account Breaches
Hackers gain access to centralized exchange accounts through weak passwords, stolen credentials, or by exploiting platform vulnerabilities.
The largest single crypto theft in history happened in February 2025 when attackers stole approximately $1.4 billion from the Bybit exchange. Chainalysis confirmed that North Korean linked hackers were responsible. Hackers stole a total of $2.67 billion from crypto platforms in 2025 according to PeckShield, a 24 percent increase from the year before.
Protecting Your Exchange Account
- Enable two factor authentication using an authenticator app, not SMS
- Use a unique strong password for every exchange account
- Withdraw funds to a personal wallet instead of leaving large amounts on exchanges
- Monitor your account for unauthorized login attempts
Blockchain security matters at every level. Even the biggest exchanges can be breached. Keeping only what you need for active trading on an exchange reduces your exposure.
Social Engineering Scams
Hackers manipulate people into sharing sensitive information like private keys, recovery phrases, or account passwords through psychological tricks.
The FBI received 181,565 crypto related complaints in 2025, up 21 percent from the previous year. Investment fraud alone caused $8.6 billion in losses, making it the single largest category of crypto crime reported by the FBI IC3.
Common Social Engineering Tactics
- Fake support teams that contact you through social media claiming a problem with your account
- Romance and investment scams that build trust over weeks before asking for crypto
- Impersonation of celebrities or influencers offering fake investment opportunities
- Urgent messages claiming your funds are at risk and require immediate action
No legitimate platform will ever ask for your private key or recovery phrase. If someone contacts you asking for these details, it is always a scam.
SIM Swapping Attacks
Hackers take control of your phone number by tricking your mobile carrier, then use it to bypass SMS based security checks and access your crypto accounts.
A SIM swapping attack enabled thieves to steal roughly $38 million in cryptocurrency from a single victim according to Proofpoint, which later led to a $33 million judgment against T-Mobile in 2025. The FBI tracked nearly $26 million in SIM swap losses across the US in 2024, while the UK reported a 1,055 percent surge in cases.
How to Prevent SIM Swapping
- Replace SMS two factor authentication with an authenticator app or hardware key
- Set a port out freeze or PIN with your mobile carrier if they offer it
- Use a separate phone number for financial accounts that you keep private
- Enable account alerts so you know immediately if someone tries to move your number
Your phone number acts as a master key for most online accounts. Switching to app based authentication removes the biggest advantage a SIM swap attacker has.
Smart Contract Exploits
Hackers find hidden flaws in the code that runs decentralized finance platforms and use those weaknesses to drain funds directly from smart contracts.
DeFi platforms lost $770 million to hacks in just the first four months of 2026 according to MEXC. Halborn research shows that smart contract vulnerabilities remain the leading cause of DeFi losses, with cross chain bridge exploits causing the largest single incident damages.
Reducing Smart Contract Risk
- Use only platforms that have completed independent security audits from reputable firms
- Avoid unknown or unaudited tokens and projects that promise unrealistic returns
- Diversify holdings across multiple platforms to limit exposure to any single exploit
- Monitor DeFi analytics dashboards for signs of unusual activity on platforms you use
DeFi risks and security should be part of every crypto holder’s basic knowledge. Audited platforms are safer, but no system is completely immune to new attack methods.

Why Some Security Measures Are Not Enough
Many crypto users believe that enabling two factor authentication or using a hardware wallet makes them completely safe. The reality is more complicated. The T-Mobile case shows that even users with extra security flags on their accounts can fall victim to a SIM swapping attack when carrier employees are manipulated.
Hardware wallets protect against remote malware but cannot prevent users from signing a malicious transaction on a phishing site. Social engineering attacks work because they bypass technology entirely and target human behavior instead. Effective cybercrime prevention requires combining multiple security layers, not relying on any single tool.
What This Means for Crypto Owners Going Forward
The $4 billion stolen in 2025 proves that crypto theft is not slowing down. The methods are evolving faster than most users can adapt. Phishing may have dropped in total losses, but individual wallet compromises surged to 158,000 incidents affecting 80,000 unique victims according to Chainalysis.
Every crypto owner needs to treat security as an ongoing practice, not a one time setup. Verify platforms before using them. Use hardware wallets for large holdings. Replace SMS authentication with stronger alternatives. These basic steps protect the majority of users from the majority of attacks.
Key Takeaways
- Hackers stole over $4 billion in cryptocurrency during 2025, a new all time record.
- Phishing remains the most common attack method despite an 83 percent drop in losses.
- Clipboard hijacking malware like MassJacker affected over 778,000 transactions.
- A single SIM swapping attack led to $38 million in stolen crypto in 2025.
- DeFi platforms lost $770 million in the first four months of 2026 alone.
- No single security tool is enough. Layer your defenses for real protection.


