CSRF Attacks Explained: How Hackers Make You Click Malicious Links
CSRF attacks are web security vulnerabilities that trick users into performing actions they never intended. Attackers send malicious links or hidden requests that execute using the victim active session. Many web applications trust browser requests without verifying their origin. Security research shows that cross site request forgery vulnerabilities still appear in poorly protected applications.
Modern web platforms manage payments, account settings, and sensitive personal data. Unauthorized actions triggered through CSRF attacks can change this information without user awareness. Organizations that fail to protect user sessions risk financial loss and reputation damage. Security teams must understand how CSRF attacks work to protect applications and users.
What Are CSRF Attacks?
CSRF attacks happen when a web application does something that the user did not ask for because the user is already logged in.
A CSRF attack makes a browser send a request to a trusted website. The application does what the request says because the users session is active.
Here are some key things about CSRF attacks
- The victim is logged into a web application
- The browser sends session cookies
- A hidden request does something
- The server does what the request says without checking
For example a user logs into their banking platform.
An attacker sends a link that silently asks for a transfer.
The server does what the request says because the session cookie looks valid.
Why Are CSRF Attacks Dangerous for Web Applications?
CSRF attacks are dangerous because attackers can do things using a victims authenticated session.
The attacker does not need to log into the account. The browser sends session cookies with the request.
Attackers often target actions like
- Changing account email addresses
- Updating account passwords
- Starting financial transactions
- Changing account settings
Studies from OWASP show that vulnerabilities in sessions are still a big risk for web applications.
Organizations that let critical operations happen without checking requests risk unauthorized transactions and data changes.
How Do Hackers Launch CSRF Attacks?
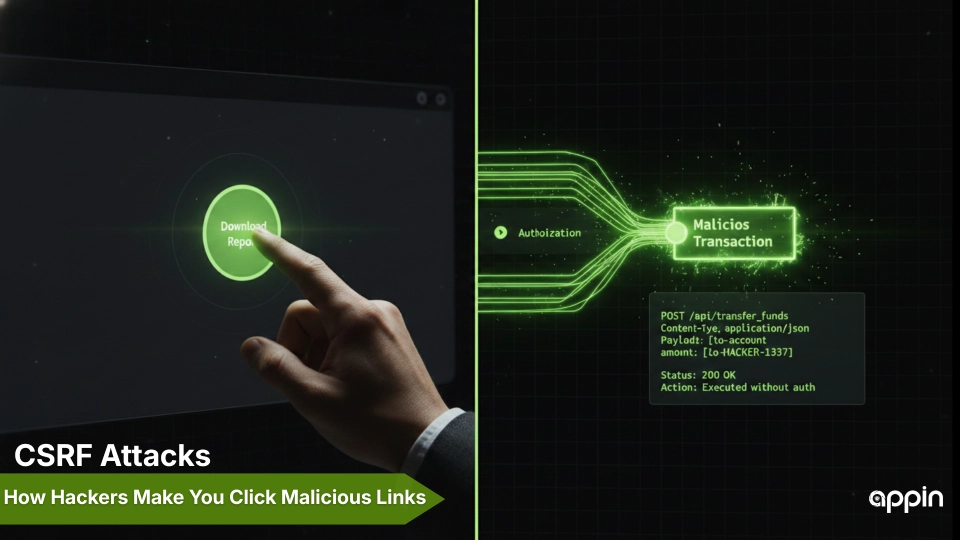
Hackers launch CSRF attacks by making bad requests that run in a victims browser.
Attackers use engineering to make users open infected links or web pages.
Here are some common techniques used in CSRF attacks
- links sent through email
- Hidden forms in web pages
- Images that trigger background requests
- Scripts placed in third-party websites
For example a victim visits a web page controlled by the attacker.
The page has a request that targets another website where the victim is logged in.
Security testers often analyze how browser requests behave during testing. Tools that help researchers intercept traffic and modify requests during security assessments are explained in guides about intercepting and modifying web requests during penetration testing
What Are Common Examples of CSRF Attacks in Web Applications?
CSRF attacks often target actions that change user data.
Attackers choose operations that cause damage without needing exploitation.
Here are some common examples of CSRF attacks
- Changing account email addresses
- Triggering money transfers
- Adding administrators to accounts
- Updating user profile settings
For example an attacker creates a page that loads a hidden request to update account information.
When the victim opens the page the request is sent using the victims browser session.
Some web applications also have risks from script injection that attackers can combine with session-based attacks. These risks are discussed in explanations of how malicious scripts manipulate browser sessions and application behavior.
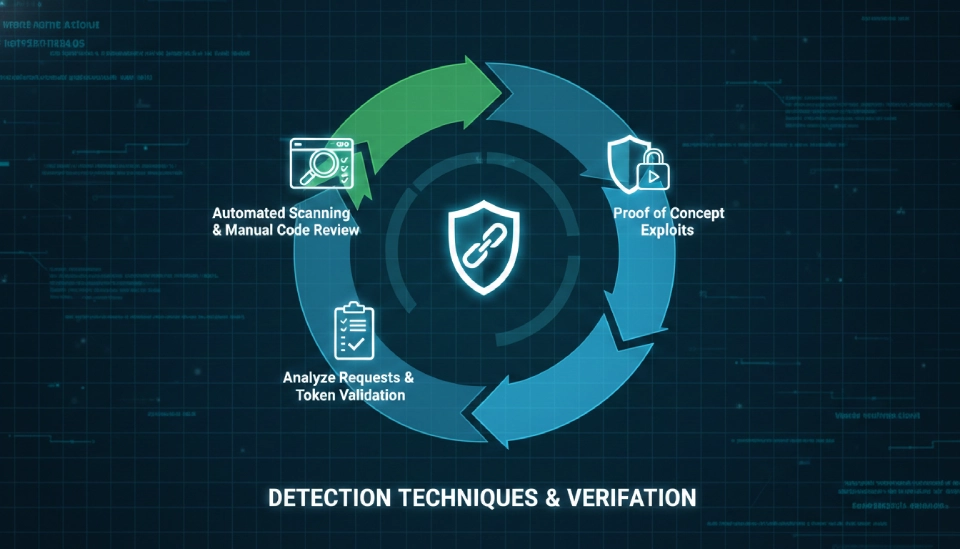
How Do Security Testers Detect CSRF Attacks?
Security testers detect CSRF attacks by analyzing requests that do operations.
Testing focuses on checking if the application validates requests before doing what they say.
Here are some common techniques for detecting CSRF attacks
- Finding requests that change user data
- Checking if CSRF tokens exist
- Verifying mechanisms for validating origins
- Testing user workflows manually
Professional security teams simulate attack scenarios during testing. This helps identify vulnerabilities that automated scanners may not find.
Organizations that do security testing reduce the risk of session-based attacks.
How Can Developers Prevent CSRF Attacks?
Developers can prevent CSRF attacks by checking every request that does a sensitive action.
Applications must verify that requests come from sources.
Here are some effective ways to prevent CSRF attacks
- Use CSRF tokens in requests
- Validate the origin and referrer headers of requests
- Require confirmation for critical actions
- Monitor unusual account activity
Secure development practices help organizations prevent unauthorized account changes and transactions.
Continuous security testing ensures that protection mechanisms stay effective as applications change.
Key Takeaways
- CSRF attacks trick users into doing things without their knowledge.
- Attackers use trusted browser sessions to send unauthorized requests.
- Financial operations and account settings are targets.
- Security testers analyze application requests to find protections.
- Developers can prevent CSRF attacks using CSRF tokens and request validation.